Protect Your Online Identity: The Importance of IP Address Security Protection
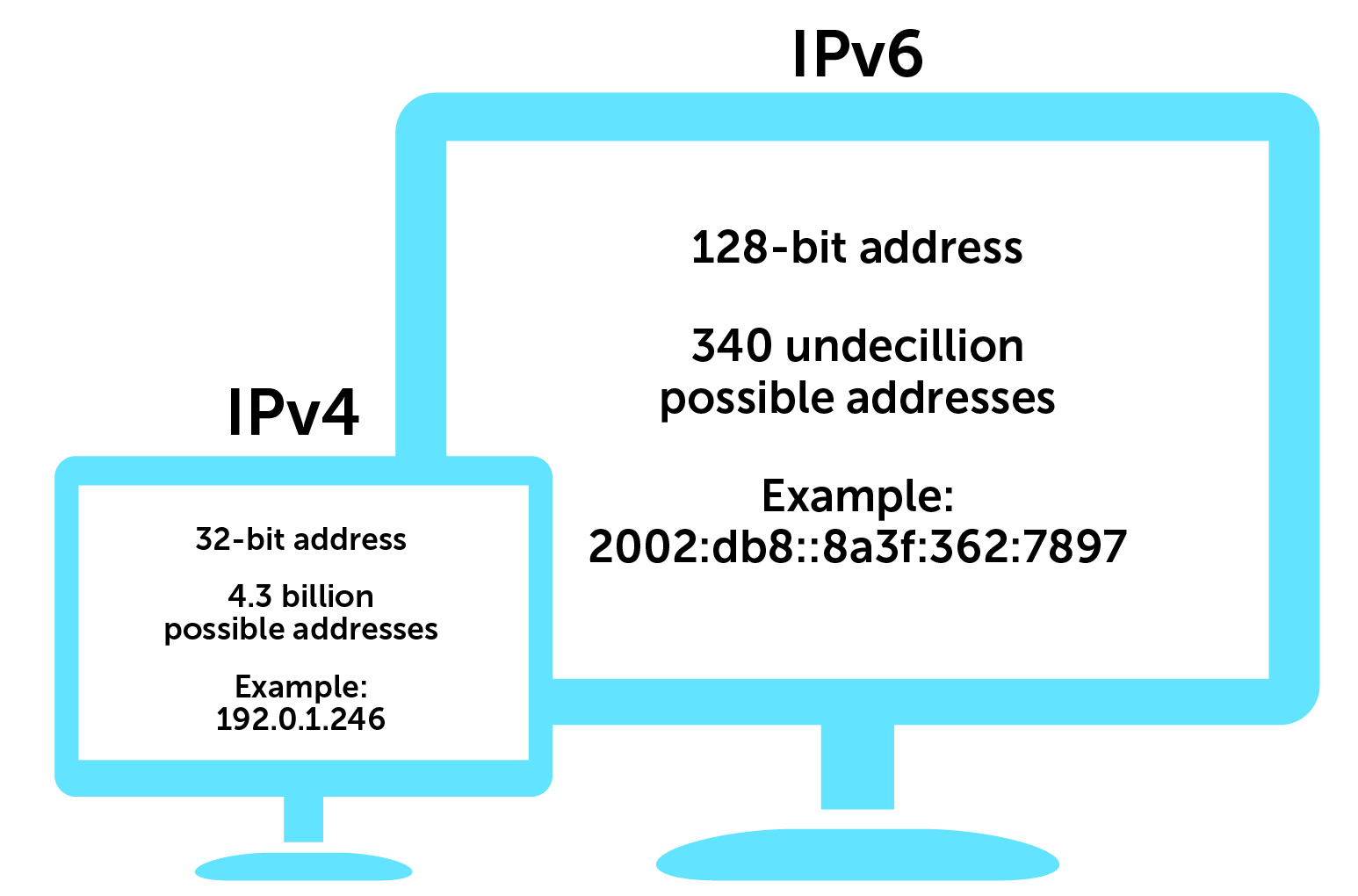
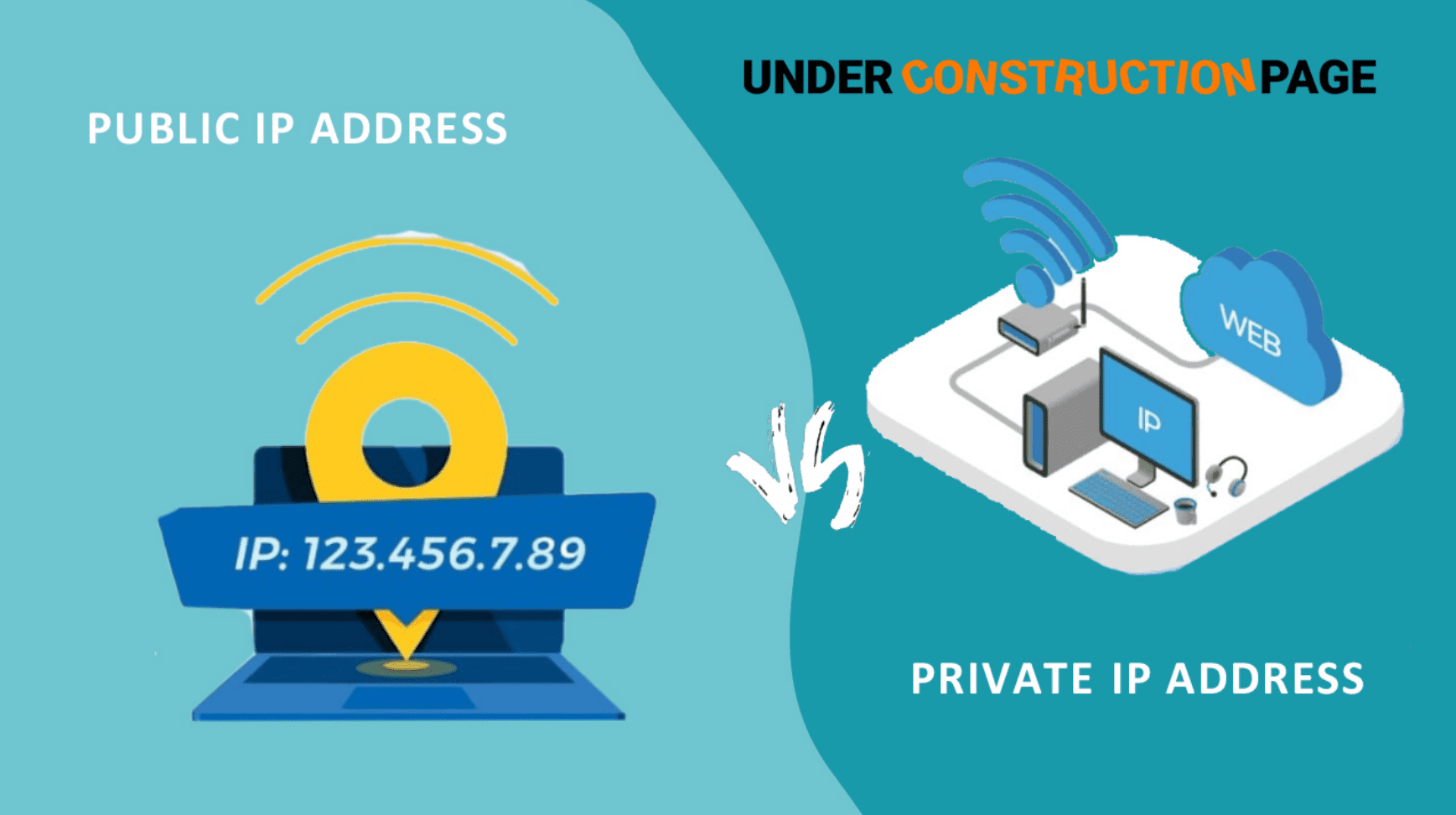
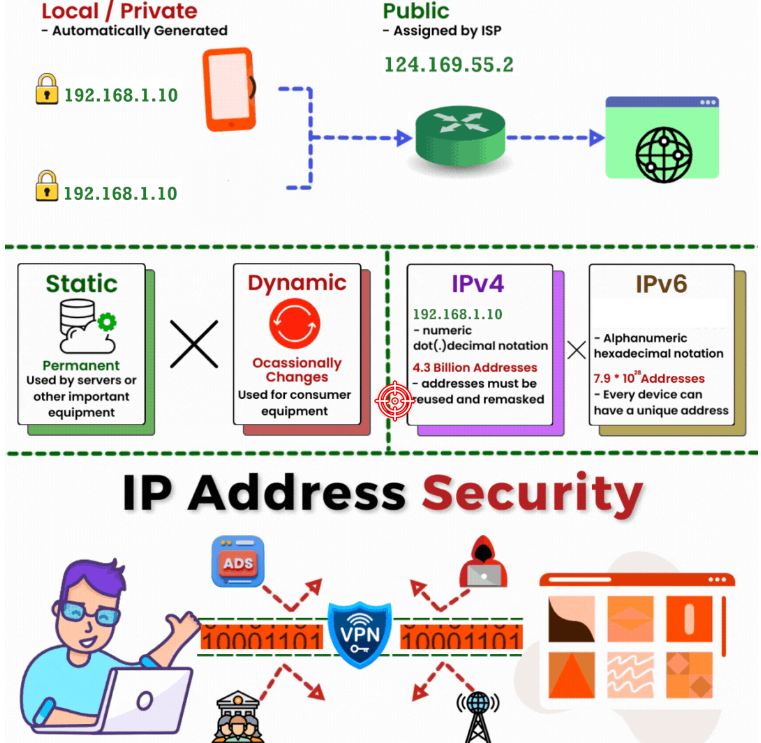
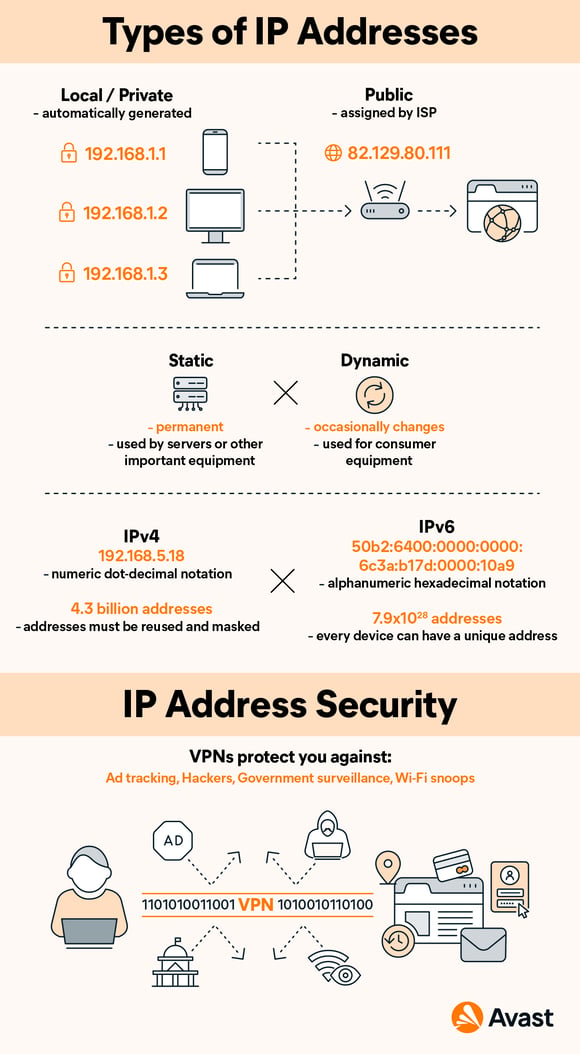
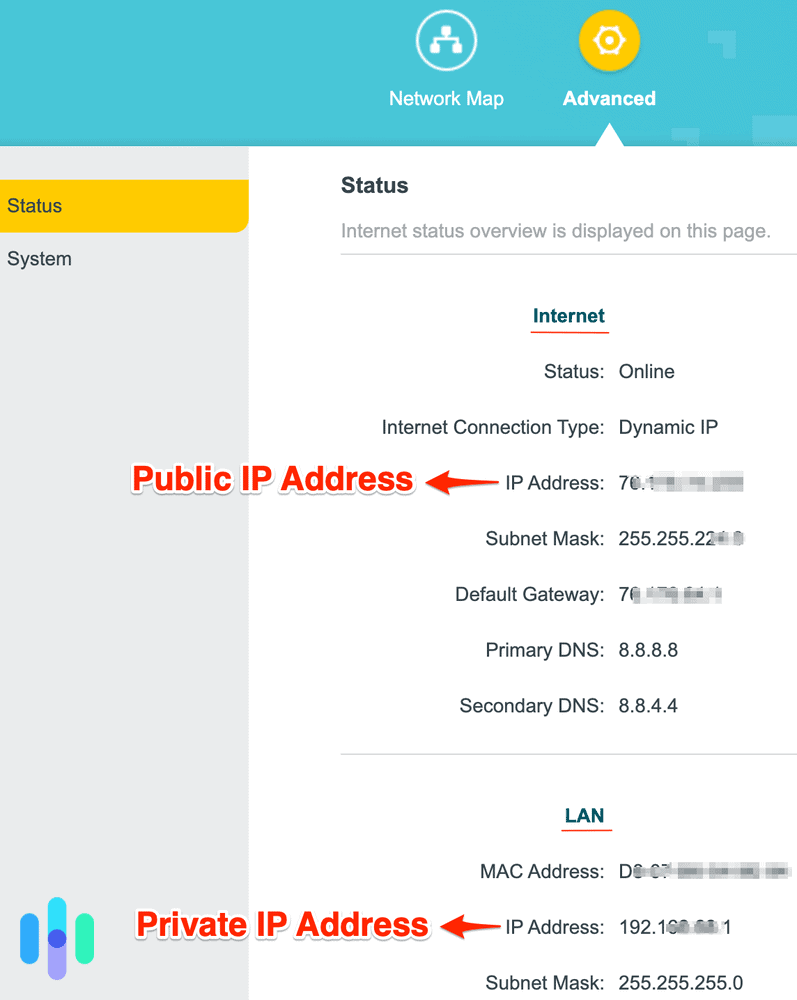
In today's digital age, our online activities are as essential as ever. We use the internet for everything from work, entertainment, to communication. With the rise of online threats, it's crucial to understand the importance of IP address security protection. Your IP address is a unique numerical label assigned to each device connected to a network using the Internet Protocol for communication. In this article, we will explore the basics of IP addresses, risks associated with IP address exposure, and effective security measures to protect your online identity.The Basic Concept of IP Addresses
An IP address serves two main purposes:- Identifying a device on the network
- Locating the device to enable communication with other devices over a network like the internet
- Identity theft
- Malware and viruses
- Unauthorized access to your device or network
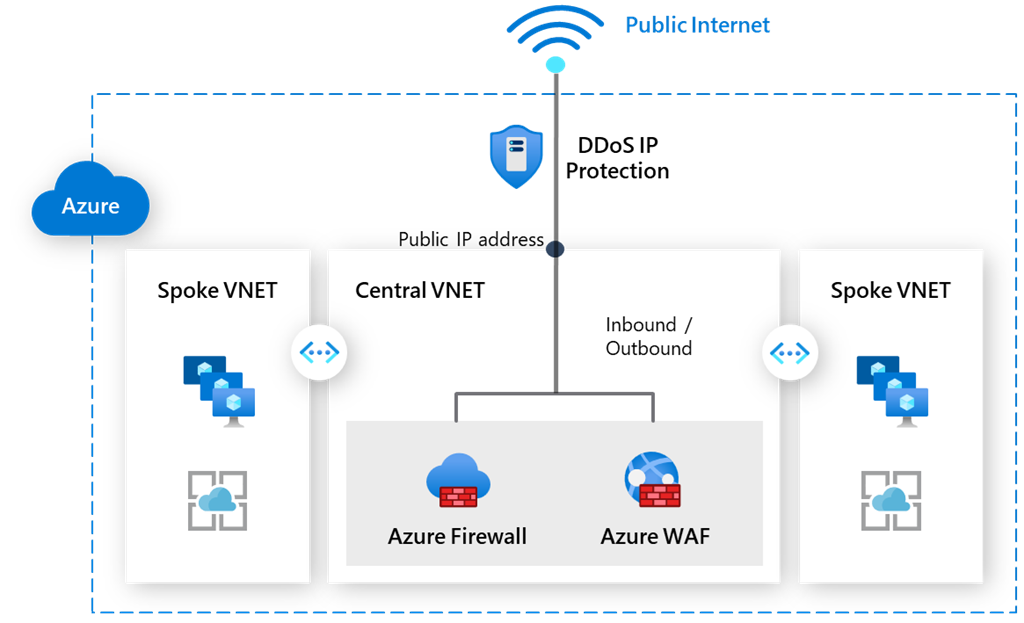
- DDoS (Distributed Denial of Service) attacks
- Data breaches and leaks

Effective Security Measures for IP Address Safety
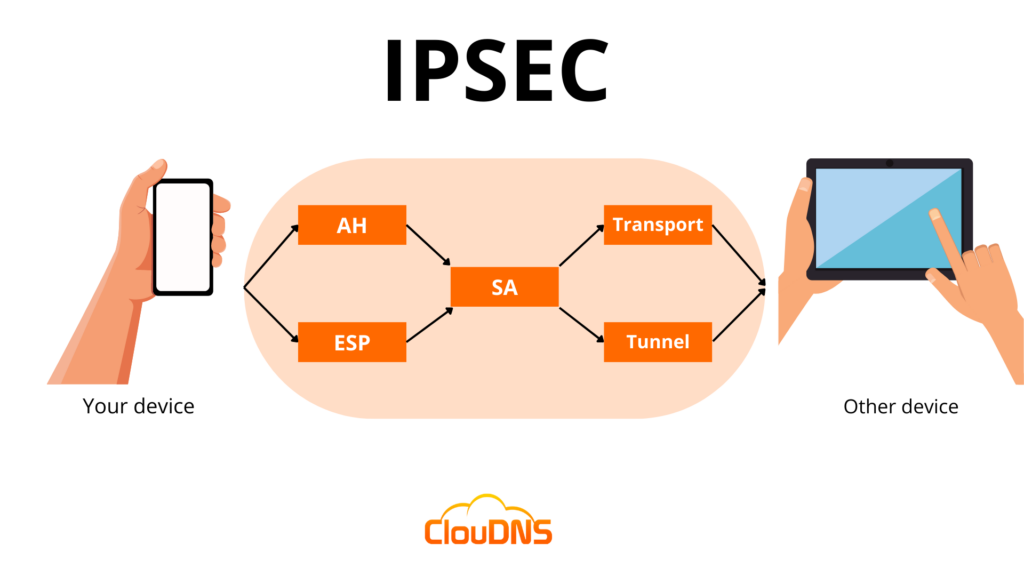
There are several methods to enhance your IP address security, including: ### **1. Virtual Private Network (VPN)** A VPN creates a secure, encrypted tunnel between your device and the internet, concealing your IP address and shielding your online activity from malicious actors. With a VPN, you can browse securely, even on public networks.Why Use a VPN?
- It encrypts your data and protects it from interception
- Hides your IP address, making it difficult for hackers to track your online activities
- Protects you from DNS spoofing and IP spoofing attacks
- Keeps your browsing history and data private

Furthermore, visual representations like the one above help us fully grasp the concept of Ip Address Security Protection.