Increase Security Against Phishing Attacks: A Comprehensive Guide
Phishing attacks have become a major threat to individuals and organizations, with the number of attacks increasing exponentially in recent years. These attacks can compromise sensitive information, disrupt business operations, and even lead to financial losses. In this article, we will discuss the importance of increasing security against phishing attacks and provide a comprehensive guide on how to protect yourself and your organization.
The Anatomy of a Phishing Attack
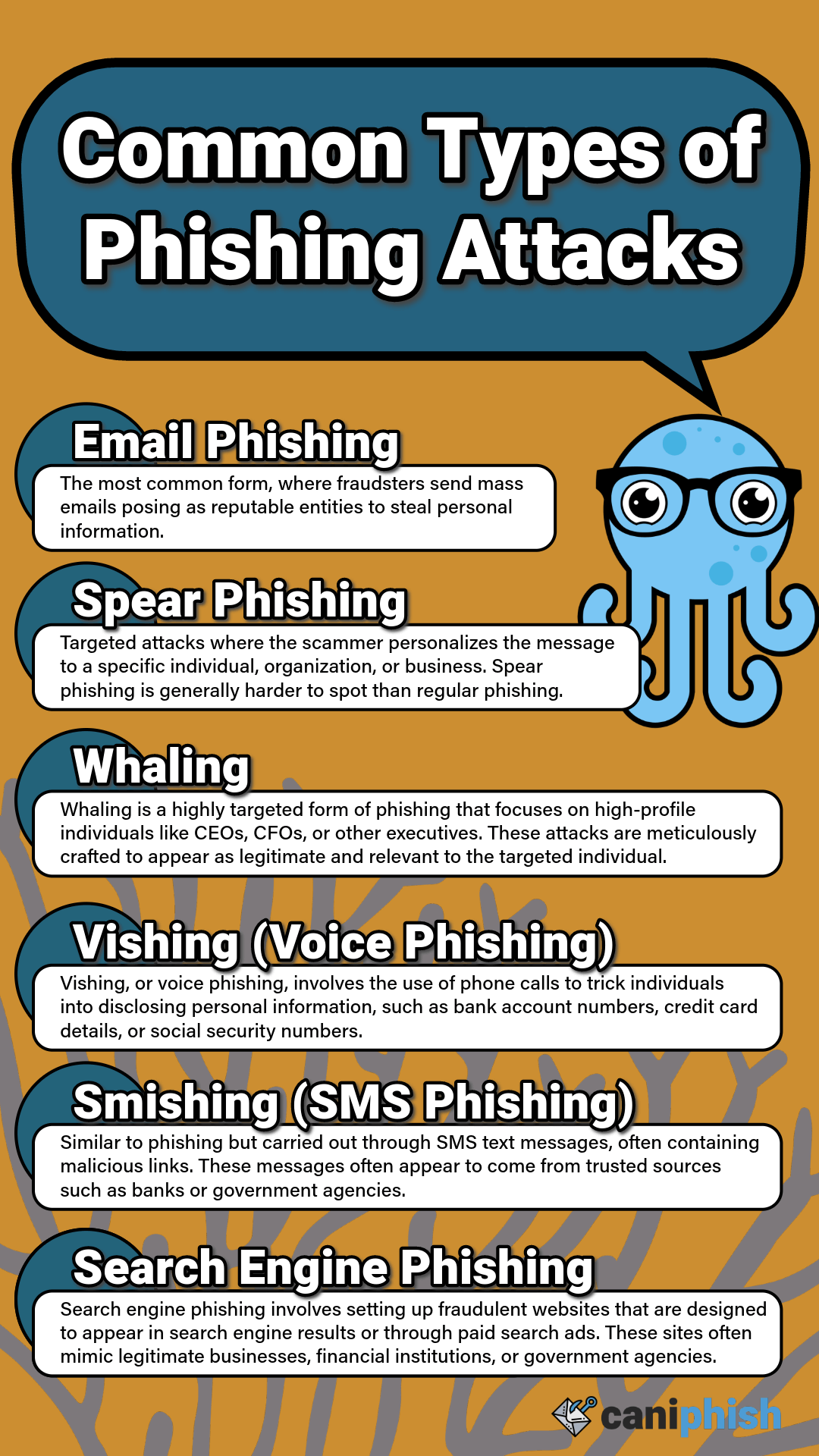
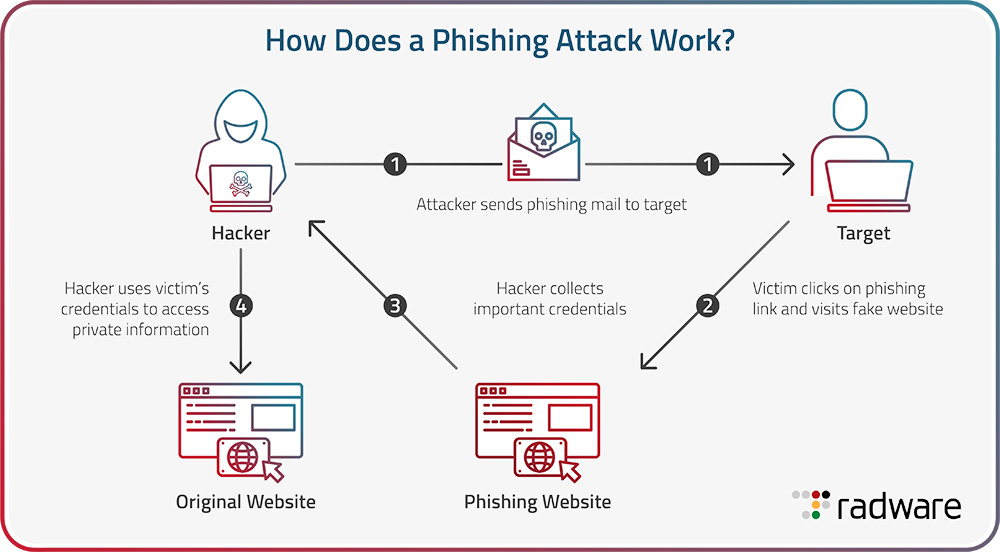
Phishing attacks typically involve the use of email or other electronic communication to trick individuals into revealing sensitive information or clicking on malicious links. These attacks can be designed to look like legitimate messages, making it difficult to distinguish between genuine and fake communications. Phishing attacks can be categorized into several types, including:
- Login credential phishing: This type of attack involves the use of email or other electronic communication to trick individuals into revealing their login credentials.
- Malware-based phishing: This type of attack involves the use of email or other electronic communication to trick individuals into downloading malware onto their device.
- Social engineering phishing: This type of attack involves the use of psychological manipulation to trick individuals into revealing sensitive information or performing certain actions.
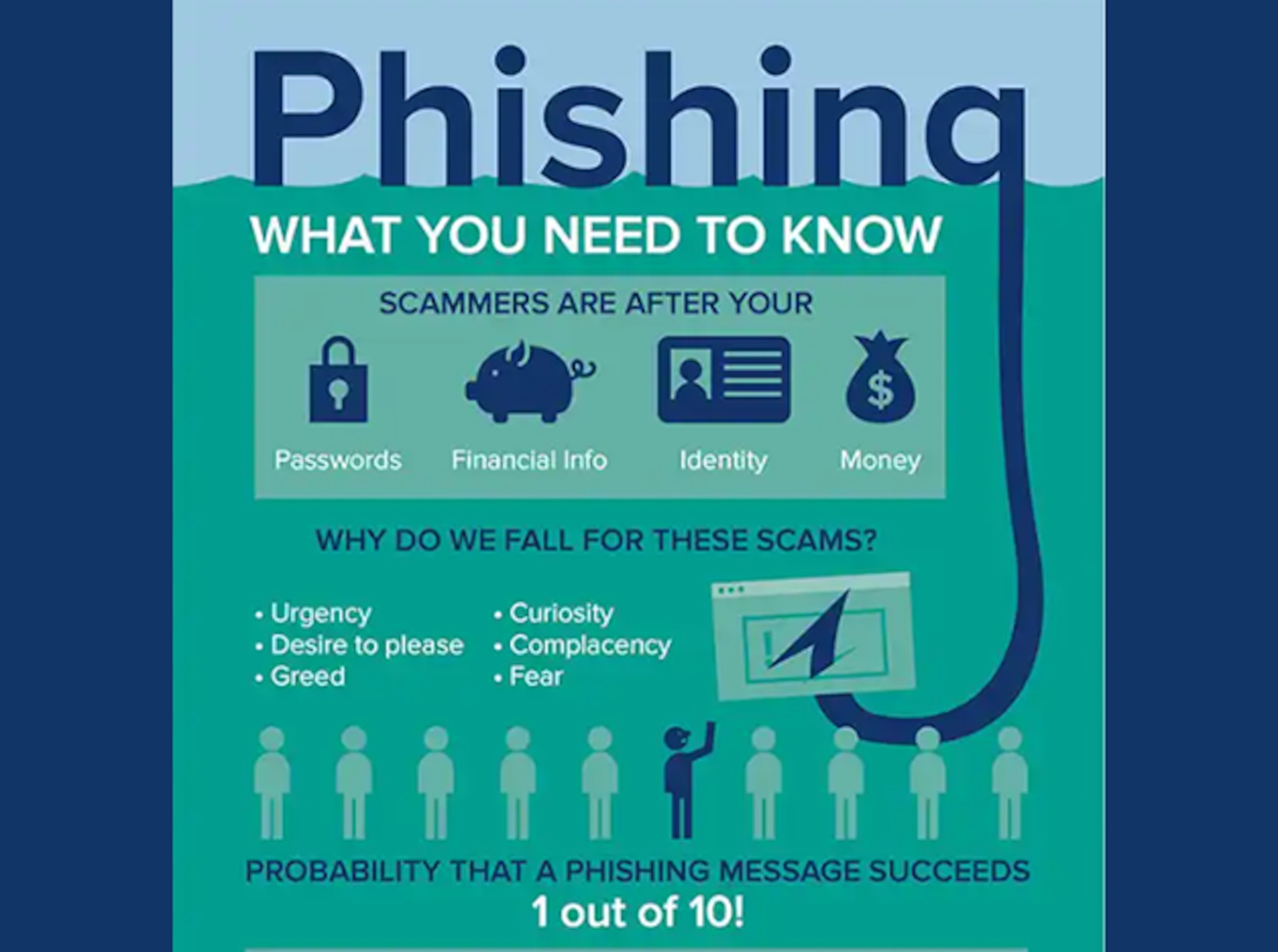
Why Phishing Attacks Are Successful
Phishing attacks are successful due to a combination of factors, including:

How to Increase Security Against Phishing Attacks
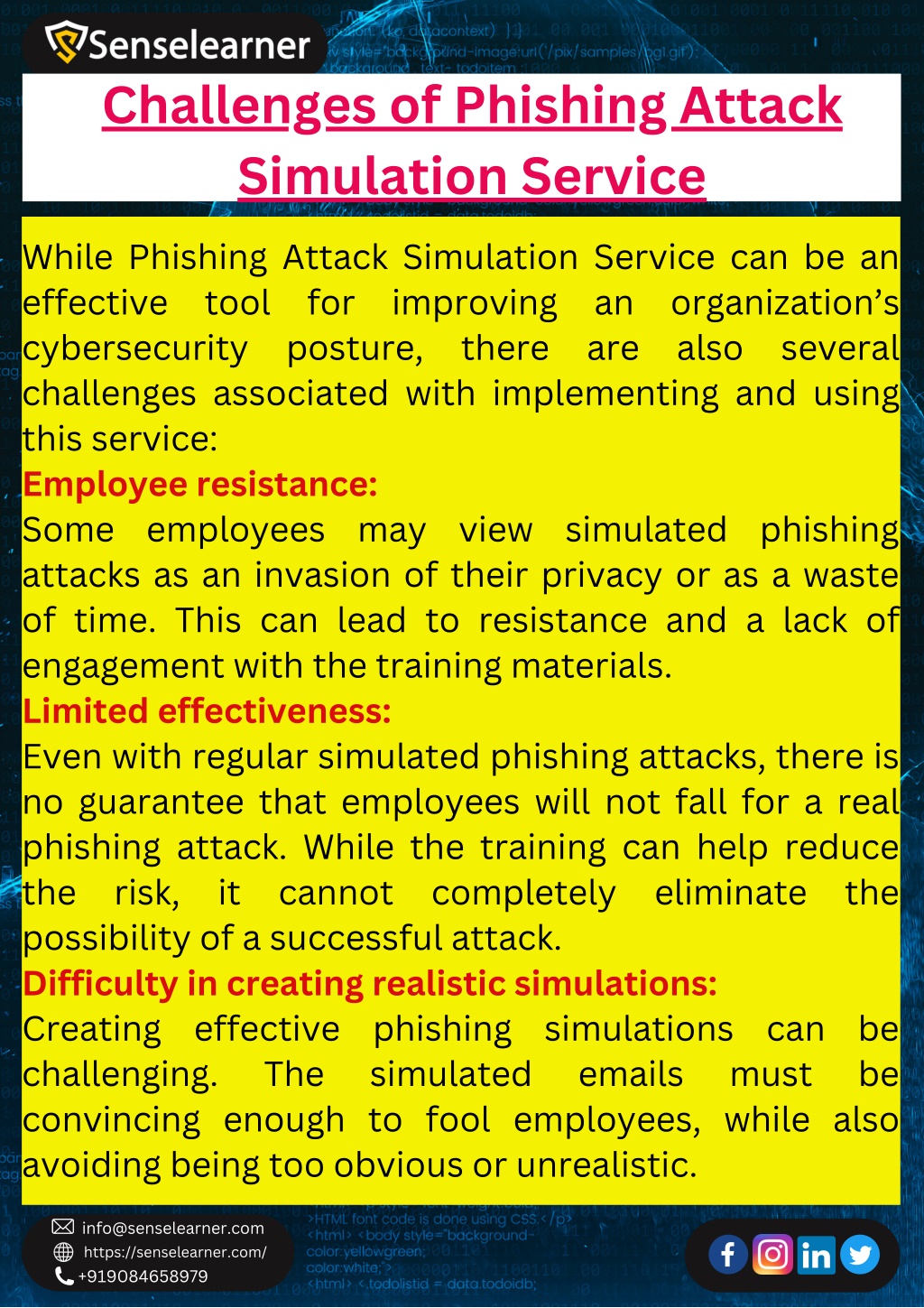
To increase security against phishing attacks, it is essential to implement a multi-layered approach that includes:
- Employee training: Educate employees on the risks associated with phishing attacks and provide them with the skills and knowledge needed to identify and respond to phishing attacks.
- Robust security software: Implement robust security software, including anti-virus and anti-malware programs, to detect and prevent phishing attacks.
- Two-factor authentication: Implement two-factor authentication to add an extra layer of security to login credentials.
- Secure email protocols: Implement secure email protocols, such as SSL/TLS, to encrypt email communications and prevent eavesdropping.
- Regular security updates: Regularly update software and systems to prevent exploitation of technical vulnerabilities.
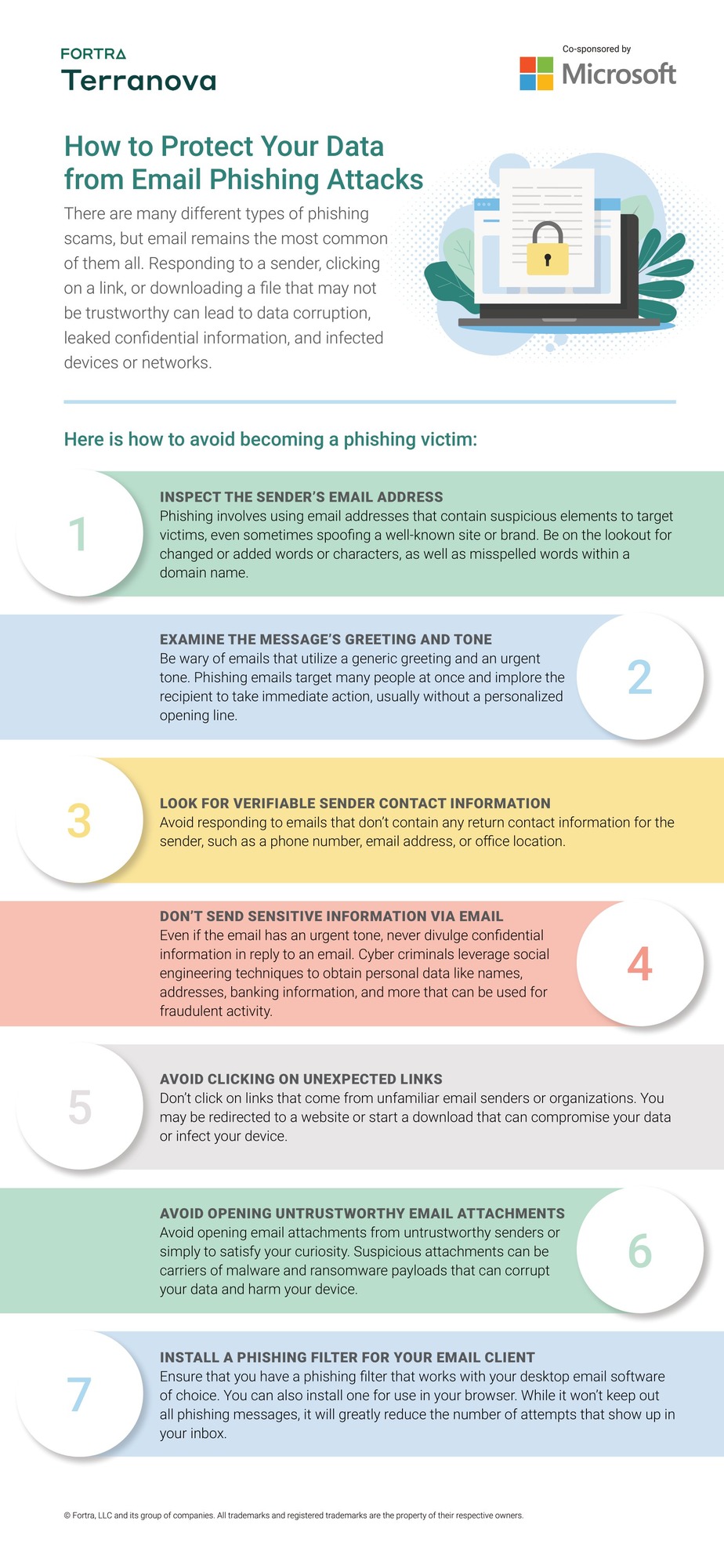
Best Practices for Avoiding Phishing Attacks
To avoid phishing attacks, it is essential to follow best practices, including:
- Verify the authenticity of emails and other electronic communications before responding or taking any action.
- Be cautious of links and attachments in emails and other electronic communications.
- Use strong and unique passwords and avoid using the same password for multiple accounts.
- Use two-factor authentication to add an extra layer of security to login credentials.
- Regularly monitor account activity and report any suspicious activity to the relevant authorities.

Conclusion
In conclusion, phishing attacks are a major threat to individuals and organizations, and it is essential to increase security against these attacks. By implementing a multi-layered approach that includes employee training, robust security software, two-factor authentication, secure email protocols, and regular security updates, individuals and organizations can protect themselves against phishing attacks. Additionally, following best practices, such as verifying the authenticity of emails and being cautious of links and attachments, can help to prevent phishing attacks. By taking these steps, individuals and organizations can reduce the risk of successful phishing attacks and protect their sensitive information.
Final Tips
Here are some final tips to help you increase security against phishing attacks:
- Regularly back up important data to prevent losses in case of a successful phishing attack.
- Use a reputable antivirus program to detect and prevent malware-based phishing attacks.
- Implement a secure password manager to generate and store unique and strong passwords.
- Use a VPN to encrypt internet communications and prevent eavesdropping.
- Report any suspicious activity to the relevant authorities and take immediate action to prevent further damage.