Understanding IP Address Spoofing Protection: A Comprehensive Guide
IP address spoofing is a malicious technique used by cybercriminals to manipulate internet data. In this article, we will delve into the world of IP address spoofing, exploring what it is, how it works, and the importance of IP address spoofing protection.
What is IP Address Spoofing?
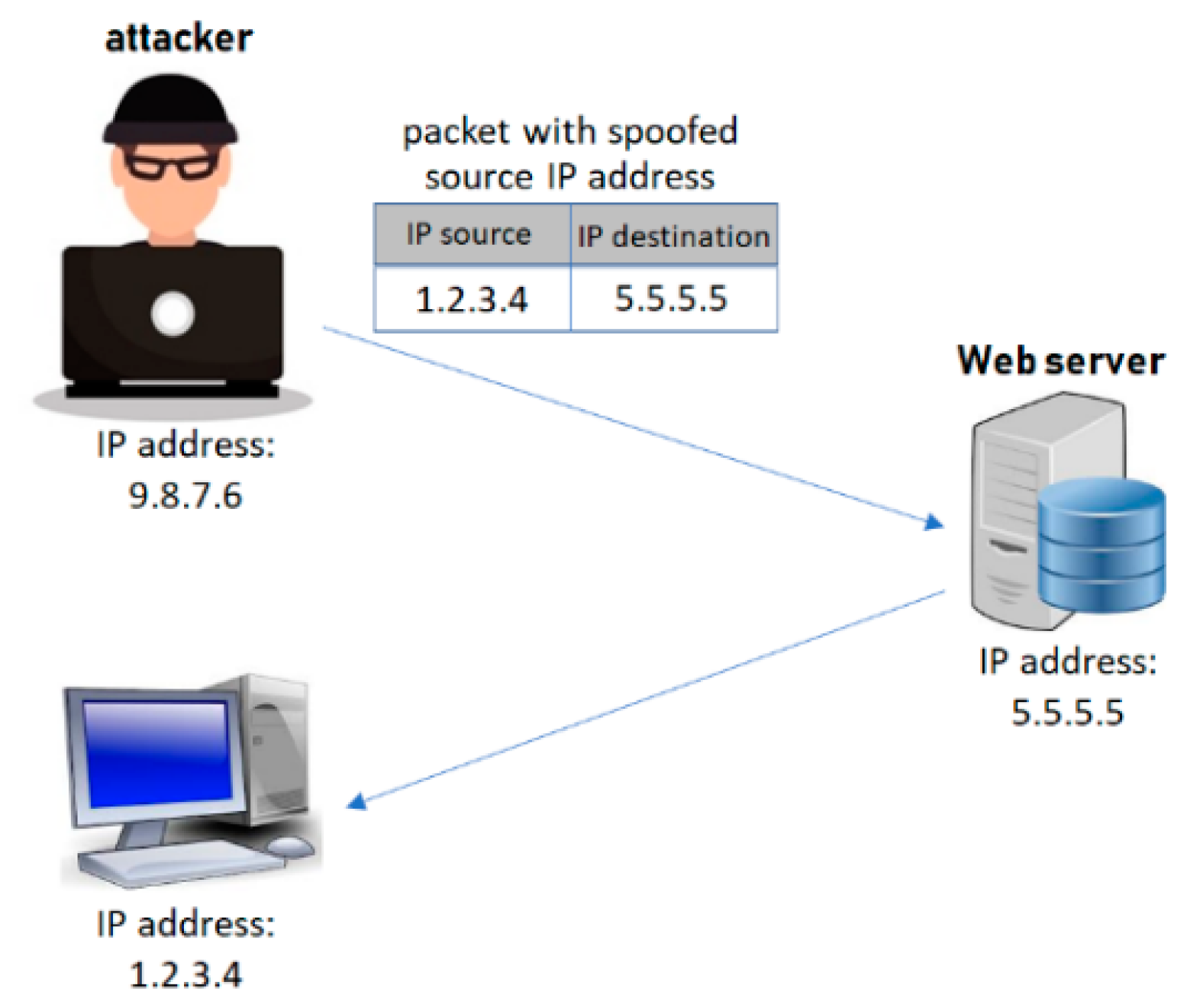
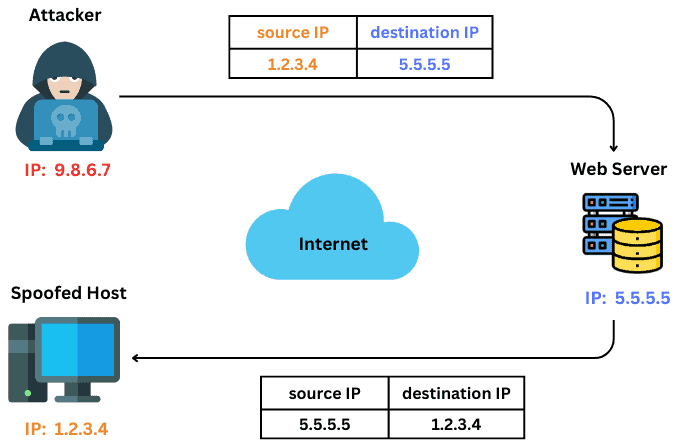
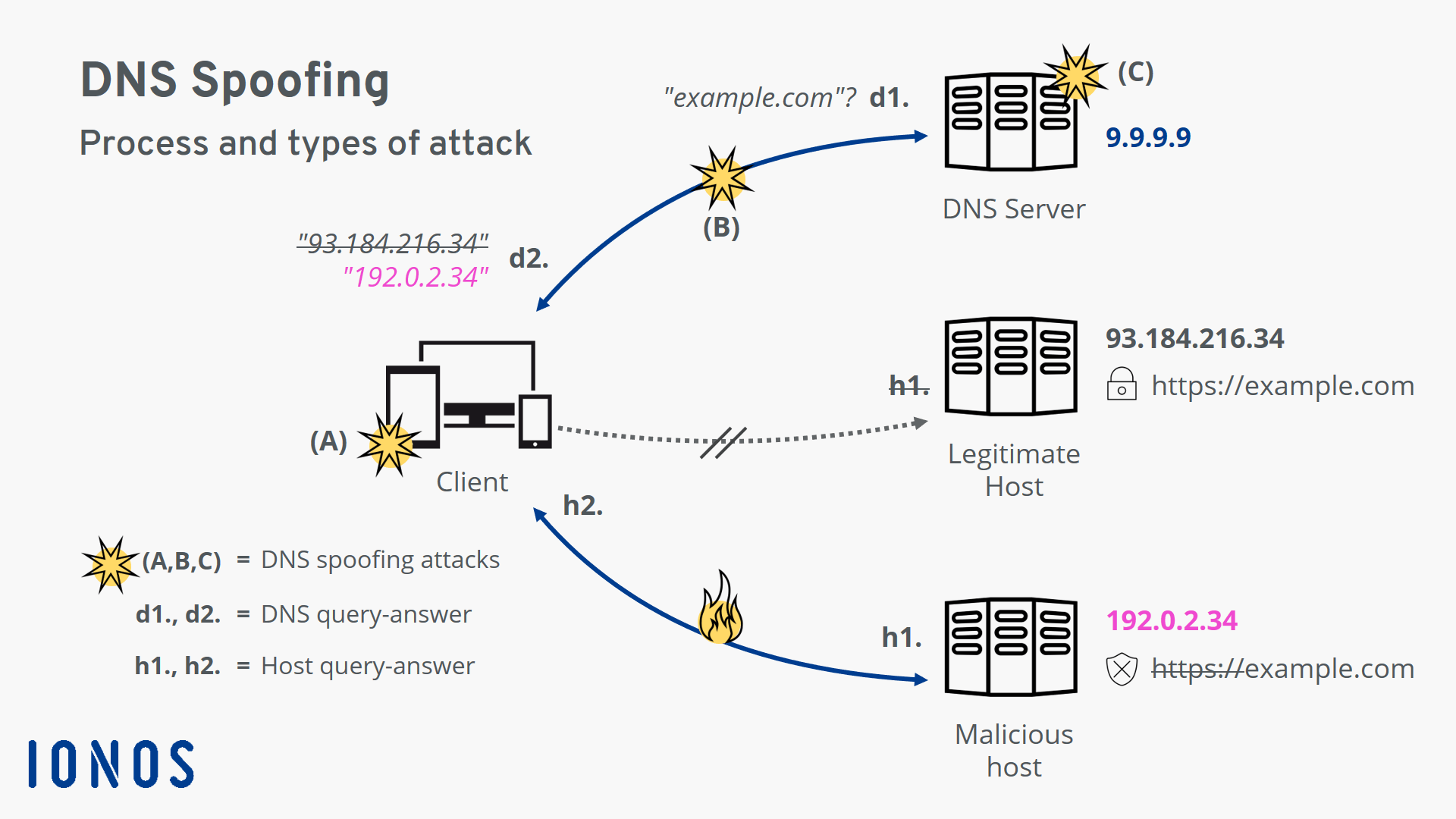
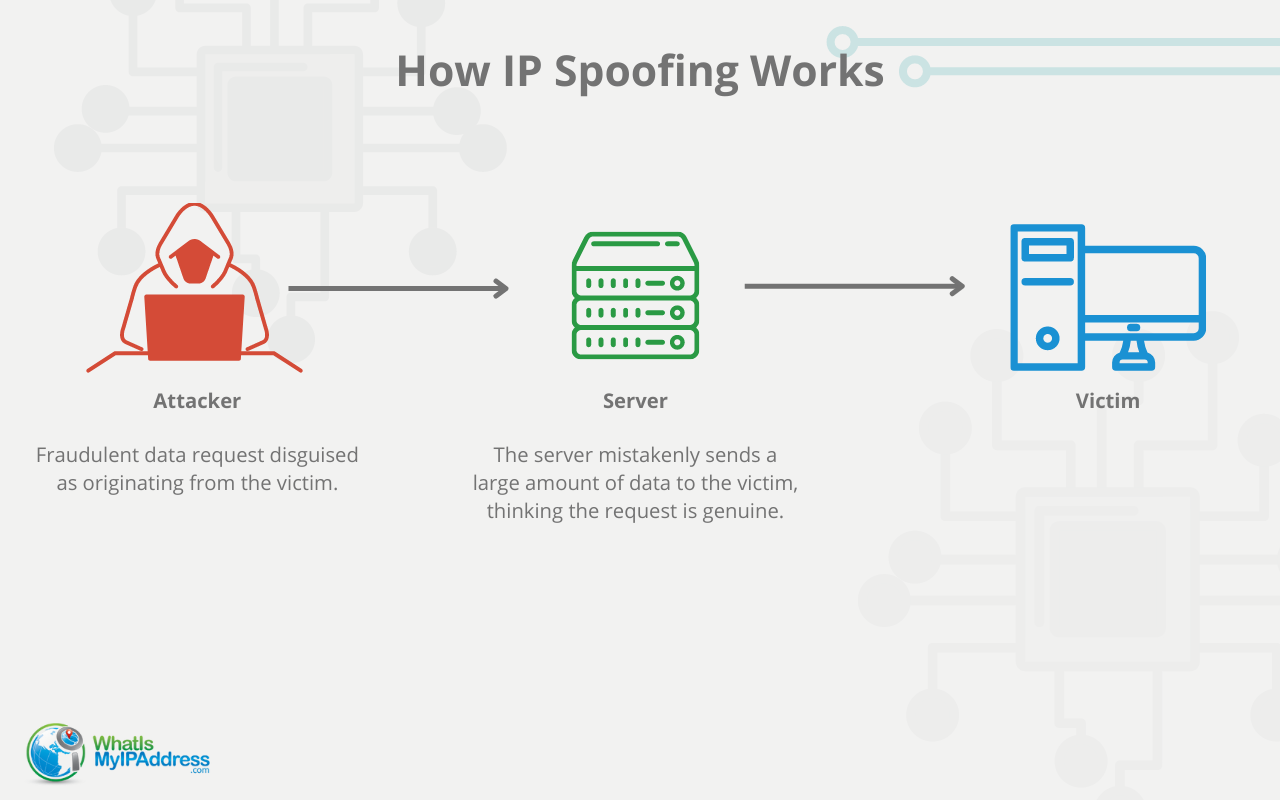
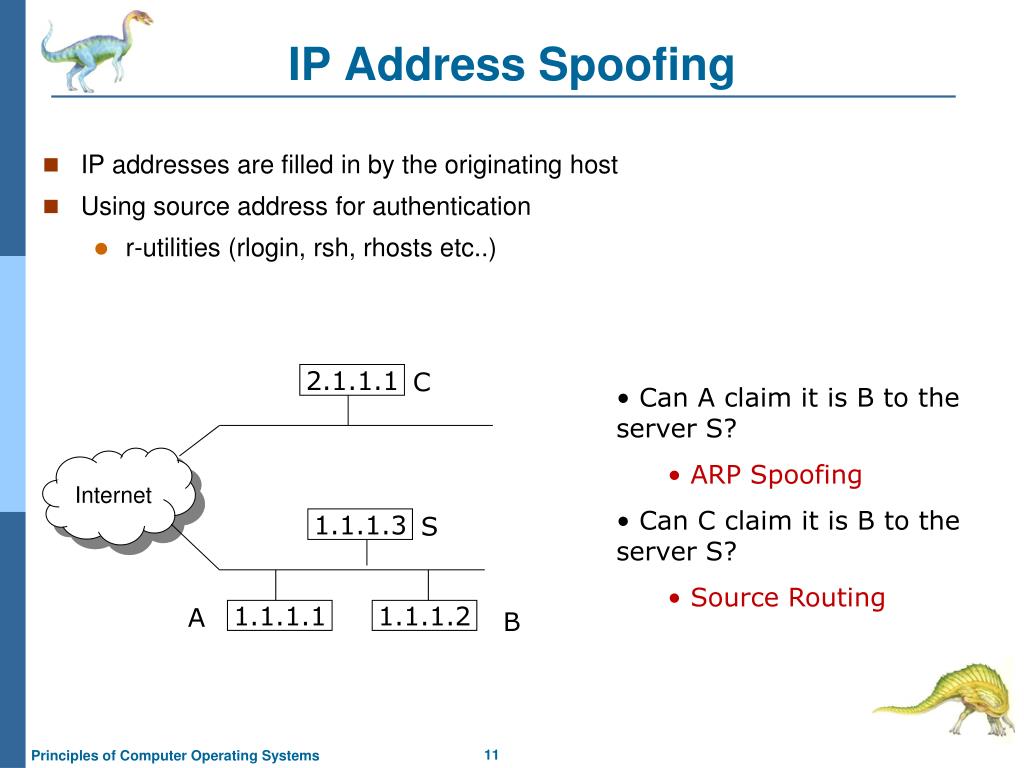
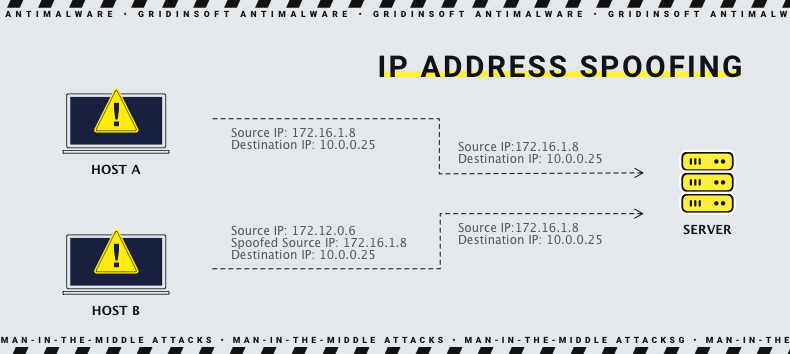
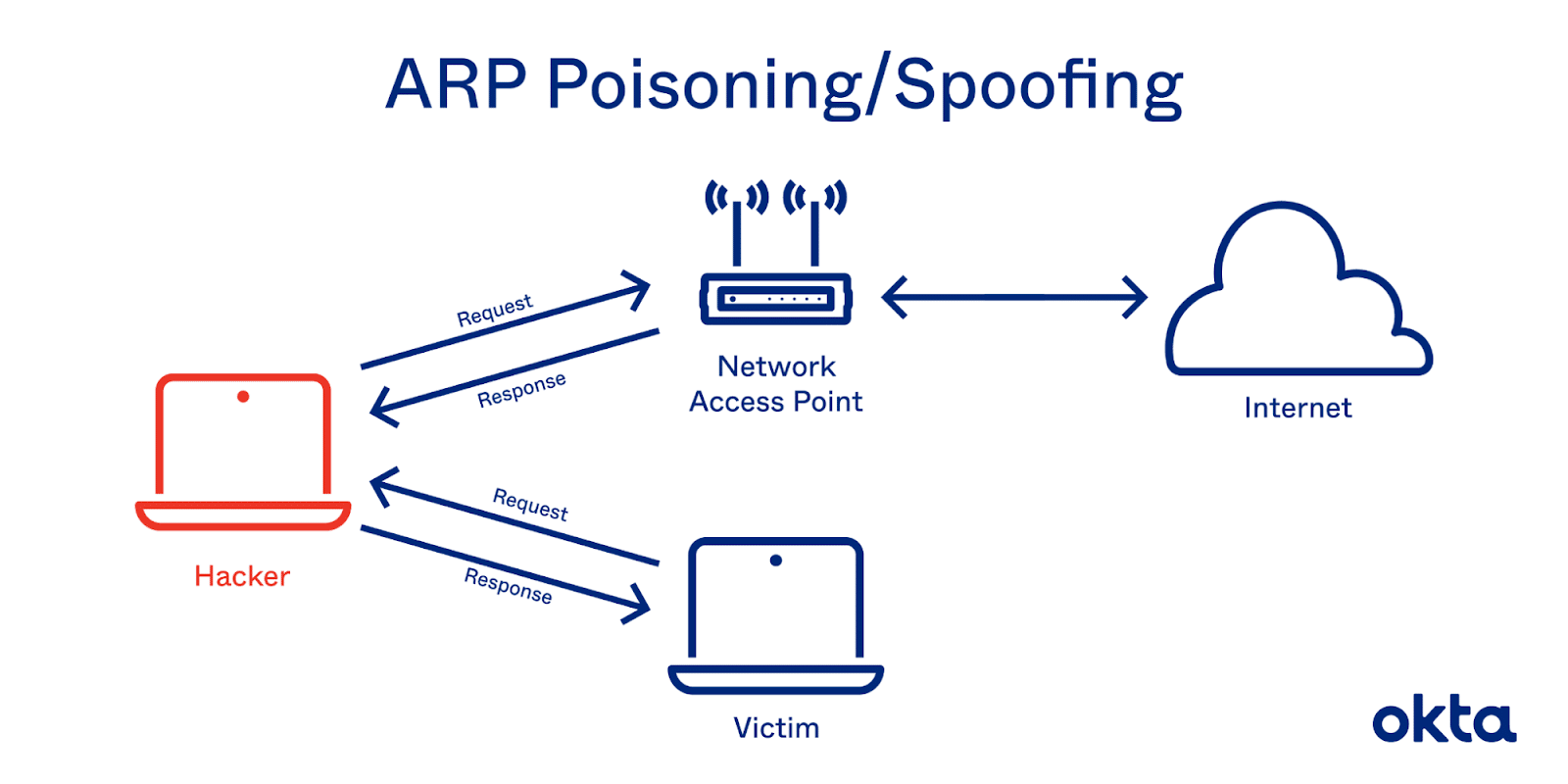
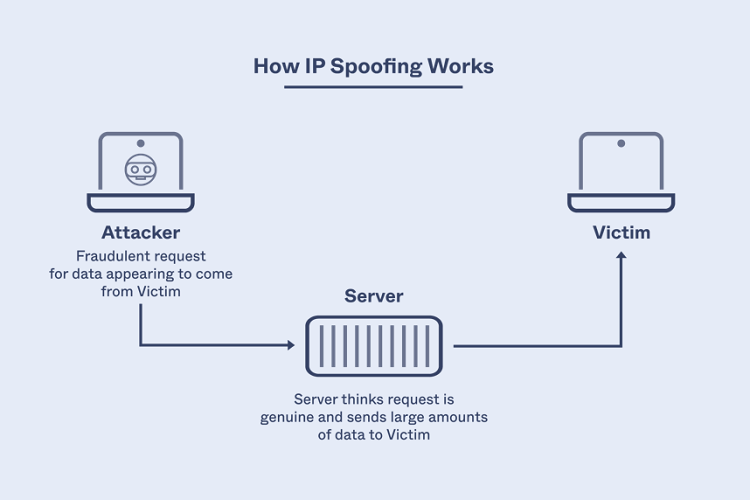
IP address spoofing is a type of malicious attack where the threat actor hides the true source of IP packets to make it difficult to know where they came from. The attacker creates packets, changing the source IP address to impersonate a different computer system, disguise the sender's identity or both.
IP address spoofing involves creating IP packets with a false source IP address, for the purpose of impersonating another computing system. This is achieved by altering the IP header, which contains information about the sender's IP address, destination IP address, and other relevant details. The attacker can use various tools and techniques to modify the IP header and create spoofed IP packets.
Moving forward, it's essential to keep these visual contexts in mind when discussing Ip Address Spoofing Protection.
Risks and Consequences of IP Address Spoofing
IP address spoofing poses significant risks to individuals, organizations, and networks. Some of the risks and consequences of IP address spoofing include:
- Unauthorized access: IP address spoofing allows attackers to gain unauthorized access to networks, systems, and resources.
- Data theft: Spoofed IP packets can be used to steal sensitive data, such as financial information, personal identifiable information, and confidential business data.
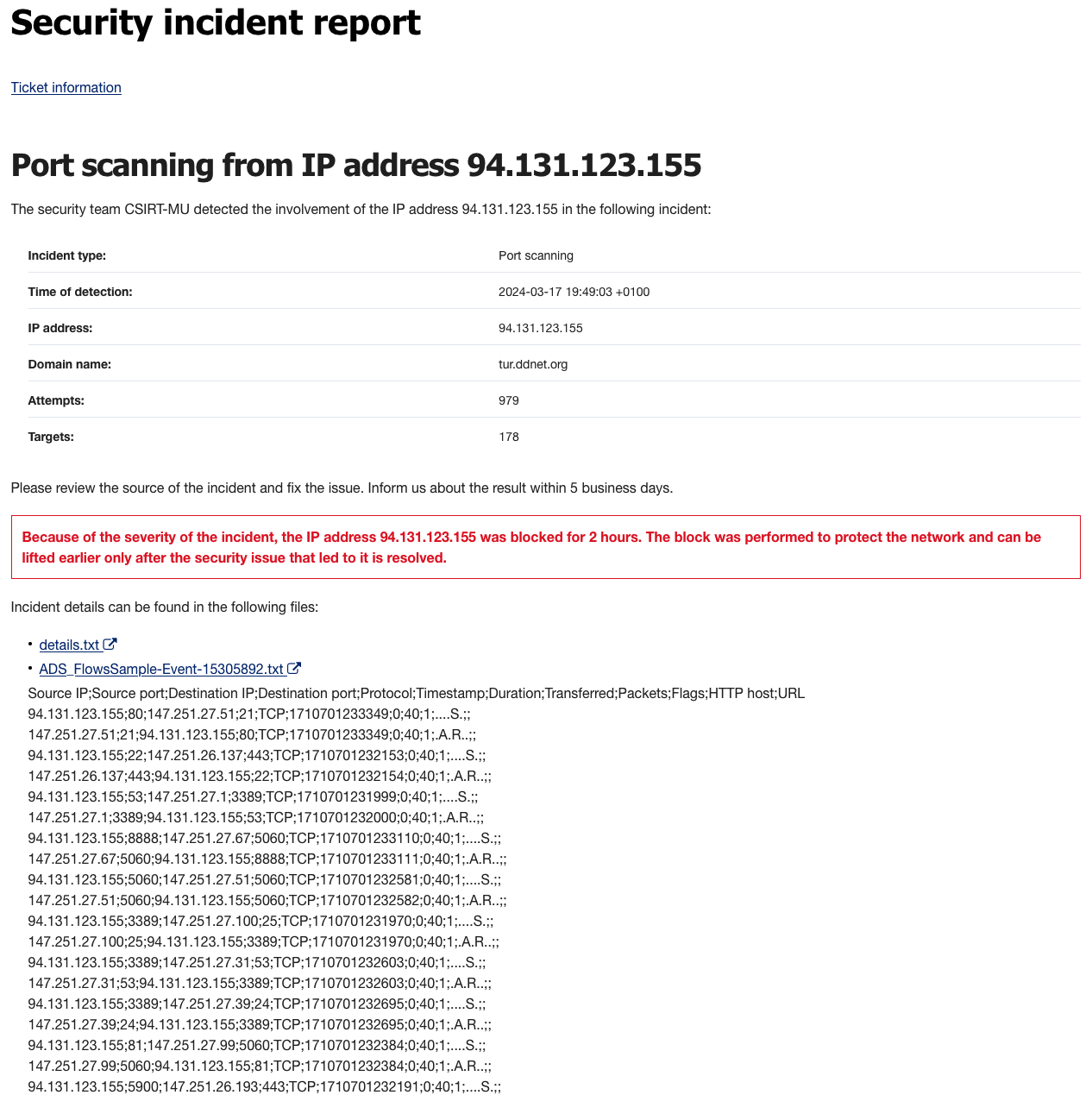
- DDoS attacks: IP address spoofing is often used to launch DDoS attacks, which can overwhelm networks and systems, causing downtime, data loss, and financial losses.
- Phishing attacks: Spoofed IP packets can be used to launch phishing attacks, which can trick recipients into divulging sensitive information or clicking on malicious links.
IP Address Spoofing Protection: Preventing and Detecting Spoofed IP Packets

This particular example perfectly highlights why Ip Address Spoofing Protection is so captivating.
IP address spoofing protection is essential in preventing and detecting spoofed IP packets. Some of the effective strategies for IP address spoofing protection include:
- Firewalls: Firewalls can be configured to block suspicious IP traffic and prevent spoofed IP packets from entering the network.
- Intrusion Detection Systems (IDS): IDS can detect and alert on suspicious network activity, including spoofed IP packets.
- Deep Packet Inspection (DPI): DPI can analyze packet headers and content to detect and prevent spoofed IP packets.
- Access Control Lists (ACLs): ACLs can be used to filter traffic based on IP addresses, ports, and protocols, preventing spoofed IP packets from entering the network.
- IP address authentication: IP address authentication can be used to verify the authenticity of IP packets and prevent spoofed IP packets from entering the network.
Best Practices for IP Address Spoofing Protection
To ensure effective IP address spoofing protection, follow these best practices:
As we can see from the illustration, Ip Address Spoofing Protection has many fascinating aspects to explore.
- Implement a robust firewall configuration.
- Use IDS and DPI to detect and prevent spoofed IP packets.
- Configure ACLs to filter traffic based on IP addresses, ports, and protocols.
- Use IP address authentication to verify the authenticity of IP packets.
- Regularly update and patch network devices and software to prevent vulnerabilities.
- Monitor network activity and logs to detect suspicious activity.
Conclusion
IP address spoofing is a malicious technique used by cybercriminals to manipulate internet data. Understanding the risks and consequences of IP address spoofing is essential in preventing and detecting spoofed IP packets. By implementing effective IP address spoofing protection strategies and following best practices, individuals and organizations can protect themselves from IP address spoofing attacks.