Ransomware Protection For Linux Server: A Comprehensive Guide
Ransomware is a significant cybersecurity threat that can compromise Linux systems, leading to data loss, downtime, and financial losses. As Linux ransomware variants continue to evolve, it's essential for organizations to adopt robust defense strategies to protect their servers and sensitive data. In this article, we'll outline the best practices for ransomware protection on Linux servers, common attack vectors, and the most effective ransomware protection software.
What is Ransomware on Linux?
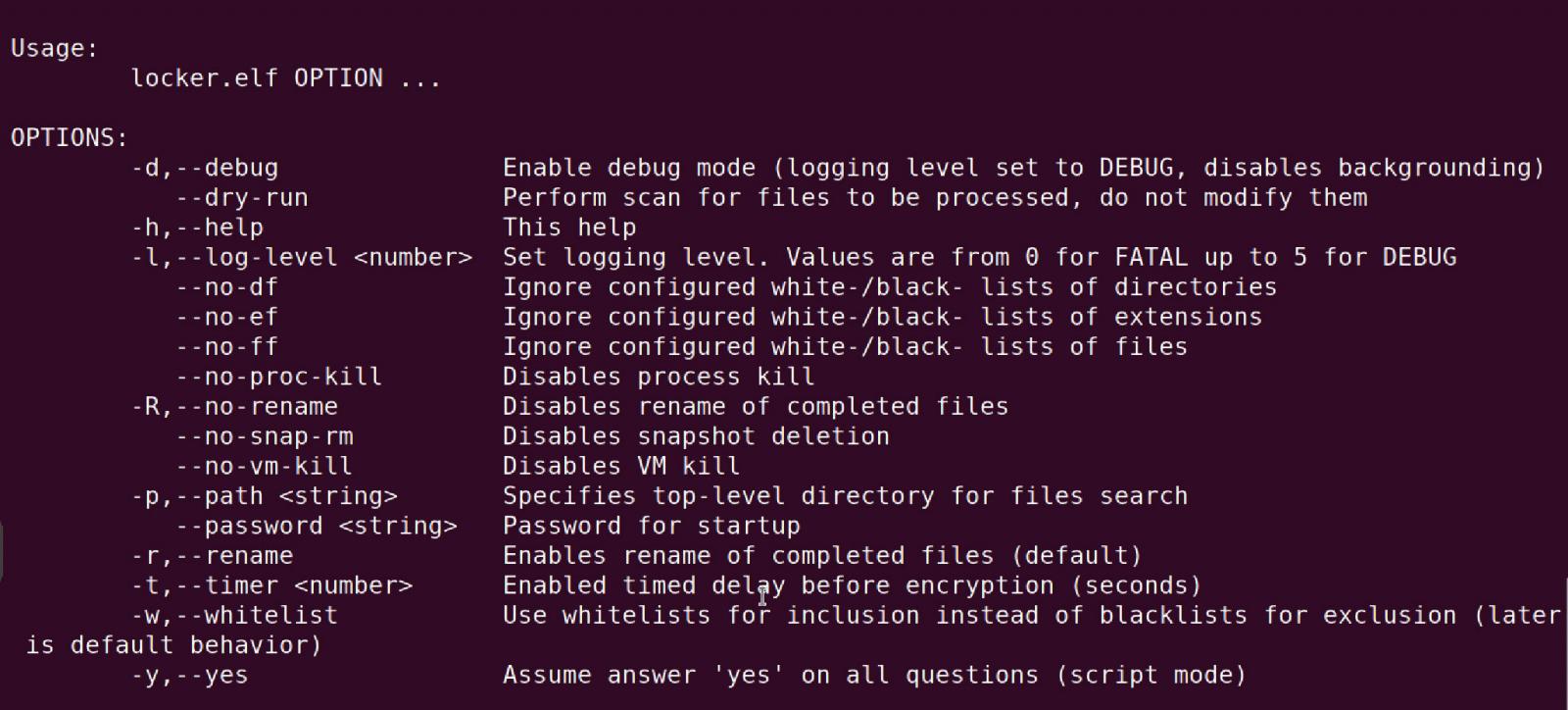
Ransomware is a type of malware that uses encryption to extort victims, causing data loss and disrupting business operations. Linux ransomware variants often target critical systems, such as servers, virtualization hosts, and cloud workloads, posing a significant risk to organizations worldwide. In recent years, attackers have been using sophisticated techniques to evade detection, making it challenging for security teams to respond effectively.
Common Ransomware Attack Vectors on Linux

As we can see from the illustration, Ransomware Protection For Linux Server has many fascinating aspects to explore.
- Unauthorized Access: Attackers may exploit vulnerabilities in Linux systems to gain unauthorized access, allowing them to deploy ransomware and encrypt sensitive data.
- Lateral Movement: Once attackers gain access, they may use techniques like SQL injection or buffer overflows to move laterally across the network, increasing the attack surface and compromising additional systems.
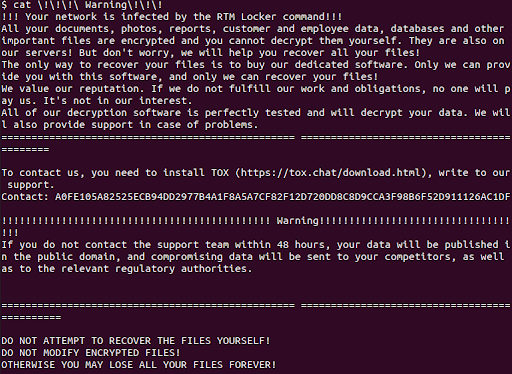
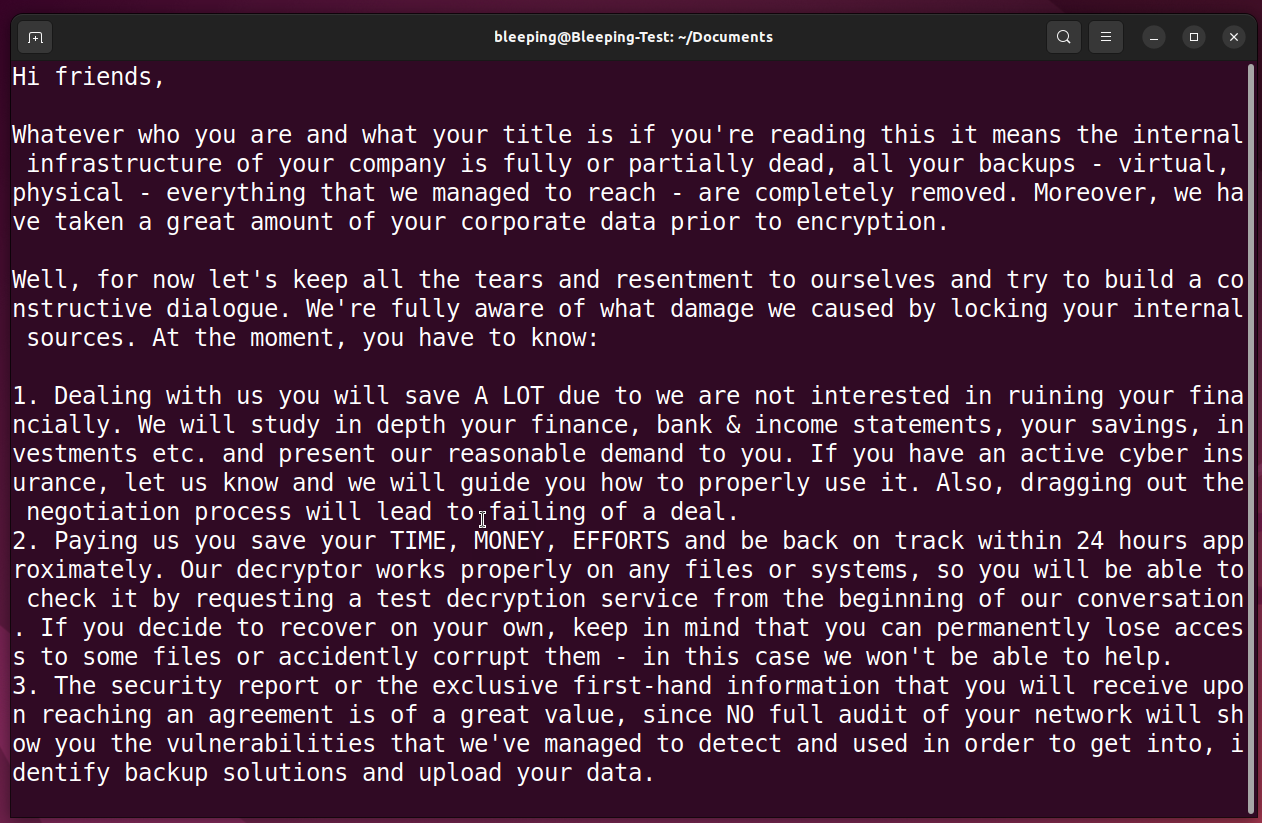
- Double Extortion: Attackers may demand ransom payments not only for decrypting the encrypted data but also for the stolen data, making recovery complex without a strong defense strategy.
Best Practices for Ransomware Protection on Linux
To prevent and mitigate ransomware attacks on Linux servers, follow these best practices:
- Implement Strong Authentication: Ensure robust authentication and authorization mechanisms are in place to prevent unauthorized access.
- Regularly Update and Patch: Keep Linux systems, including their software and firmware, up-to-date and patched to fix vulnerabilities.
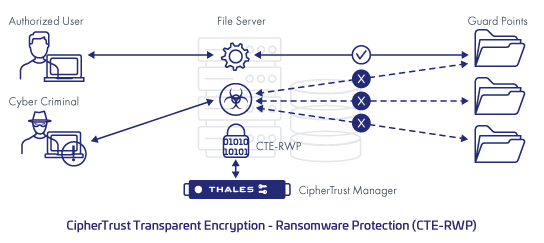
- Use Advanced Threat Detection: Implement behavior-based detection and response solutions to identify and contain potential threats.
- Implement Regular Backups: Regular backups of critical data can ensure business continuity and minimize the impact of a ransomware attack.

Several ransomware protection software solutions are available for Linux, providing robust security and mitigation capabilities. Here are some of the most effective options:
Conclusion
Linux ransomware variants continue to pose a significant threat to organizations, compromising sensitive data and disrupting business operations. By following best practices for ransomware protection on Linux, such as implementing strong authentication, regularly updating and patching, and using advanced threat detection, organizations can minimize the risk of a ransomware attack. Additionally, utilizing effective ransomware protection software solutions like Halcyon, Sophos, and Bitdefender can provide robust security and mitigation capabilities, ensuring business continuity and minimizing downtime.
Additional Resources

Such details provide a deeper understanding and appreciation for Ransomware Protection For Linux Server.
For more information on ransomware protection on Linux, consult the following resources:
- Martello: Learn how to protect your Linux systems against ransomware with Martello's ransomware protection guide.
- Microsoft Security Response Center: Discover Microsoft's latest insights on ransomware and how to protect your organization.
- Fortra: Explore Fortra's data loss prevention (DLP) software, designed to prevent and detect sensitive data exposure across endpoints, cloud, and SaaS applications.
Stay informed and prepared to protect your Linux servers from ransomware threats. Regularly review and update your security measures to ensure the best possible defense against emerging threats.