Important Steps in Computer Security
Protecting your computer from cyber threats is essential in today's digital age. With increasing dependency on technology for personal, business, and government operations, cybersecurity has become a top priority for organizations worldwide. In this article, we will discuss the important steps in computer security that you can take to safeguard your computer and personal information.
Implementing Basic Cybersecurity Practices
The first step in protecting your computer from cyber threats is to implement basic cybersecurity practices. This includes:
- Using strong passwords: Avoid using weak passwords that can be easily guessed. Use a combination of letters, numbers, and special characters to create a strong password.
- Enabling two-factor authentication: Add an extra layer of security to your accounts by enabling two-factor authentication. This requires a code sent to your phone or email in addition to your password.
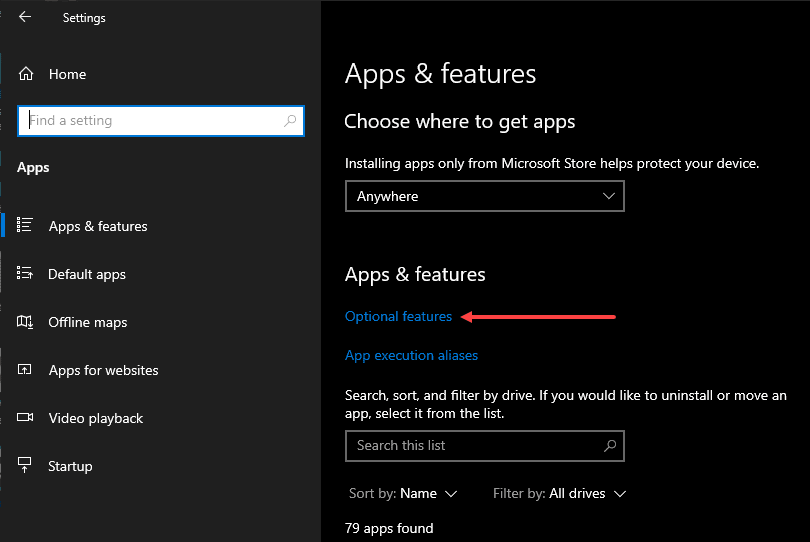
- Keeping software up-to-date: Regularly update your operating system, browser, and other software to ensure that you have the latest security patches and features.
- Using antivirus software: Install reputable antivirus software to protect your computer from malware and other cyber threats.
- Being cautious with emails and attachments: Avoid opening suspicious emails and attachments, as they can contain malware or phishing scams.
Protecting Your Data
Protecting your data is crucial in preventing cyber attacks. Follow these important steps:

Such details provide a deeper understanding and appreciation for Important Steps In Computer Security.
- Back up your data: Regularly back up your important files and data to an external hard drive, cloud storage, or both.
- Use encryption: Encrypt your data to prevent unauthorized access. This includes using encryption software and encryption protocols for data in transit.
- Use secure protocols: Use secure protocols such as HTTPS and SFTP to encrypt data in transit.
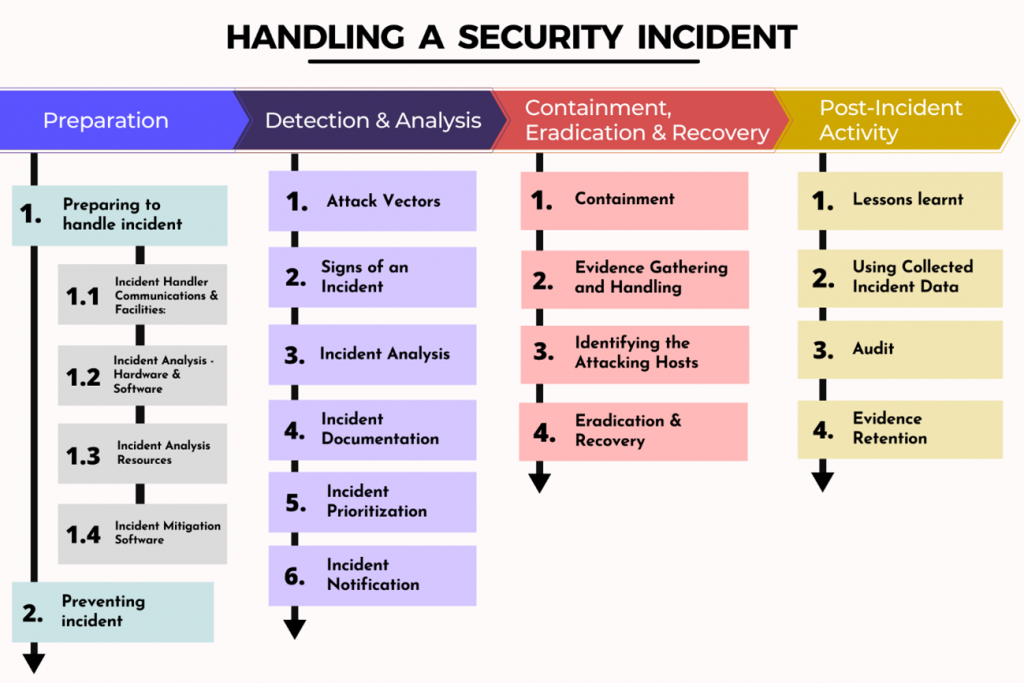
- Monitor your data: Regularly monitor your data for any suspicious activity, and report any incidents to your IT department or security team.
- Use data loss prevention tools: Use data loss prevention tools to detect and prevent data breaches.
Safe Browsing Practices
Safe browsing practices are essential in preventing cyber attacks. Follow these important steps:
- Use a reputable browser: Use a reputable browser that has built-in security features and updates regularly.
- Avoid suspicious websites: Avoid visiting suspicious websites that may contain malware or phishing scams.
- Use a VPN: Use a virtual private network (VPN) to encrypt your internet traffic and protect your data from hackers.
- Use anti-tracking software: Use anti-tracking software to prevent your browsing history and personal data from being tracked.
- Use a secure search engine: Use a secure search engine that has built-in security features and does not track your search history.
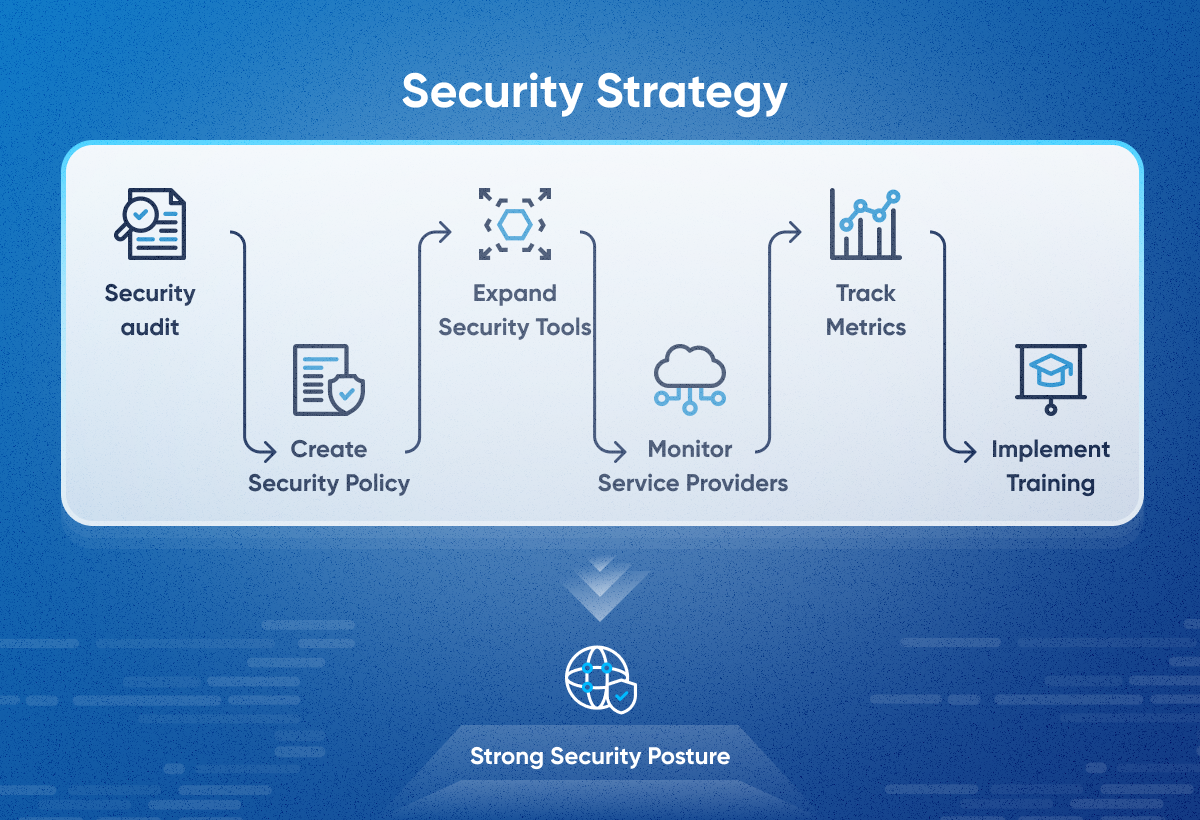
Additional Security Measures
Additionally, you can implement the following security measures to protect your computer and personal information:

- Implement role-based access control: Allow only authorized personnel to access sensitive data and systems.
- Use a firewall: Use a firewall to block unauthorized access to your computer and network.
- Use intrusion detection and prevention systems: Use intrusion detection and prevention systems to detect and prevent malware and other cyber threats.
- Use a security information and event management (SIEM) system: Use a SIEM system to monitor and analyze security-related data from various sources.
- Conduct regular security audits: Conduct regular security audits to identify vulnerabilities and improve your security posture.
Conclusion
Protecting your computer from cyber threats requires a combination of technical and non-technical measures. By implementing these important steps in computer security, you can safeguard your computer and personal information from cyber attacks. Remember to stay vigilant and update your security measures regularly to ensure that you are protected from the latest cyber threats.
Additional Resources
- Microsoft Security Response Center: www.microsoft.com/security
- National Cybersecurity Centre: www.ncsc.gov.uk
- Cybersecurity and Infrastructure Security Agency (CISA): www.cisa.gov
- National Institute of Standards and Technology (NIST): www.nist.gov
















.png)